Security and authentication

Authentication Support
LDAP / Active Directory, Kerberos,SSO/SAML 2.0, Two-factor authentication and Universal 2nd Factor (U2F) and Time-based One-Time Password (TOTP) second factor apps to increase the security of user login handling.
Existing storage and database technology
SecuredCloud supports any existing storage solution, including object store technologies, SecuredCloud works with industry standard SQL databases like PostgreSQL, MySQL and MariaDB
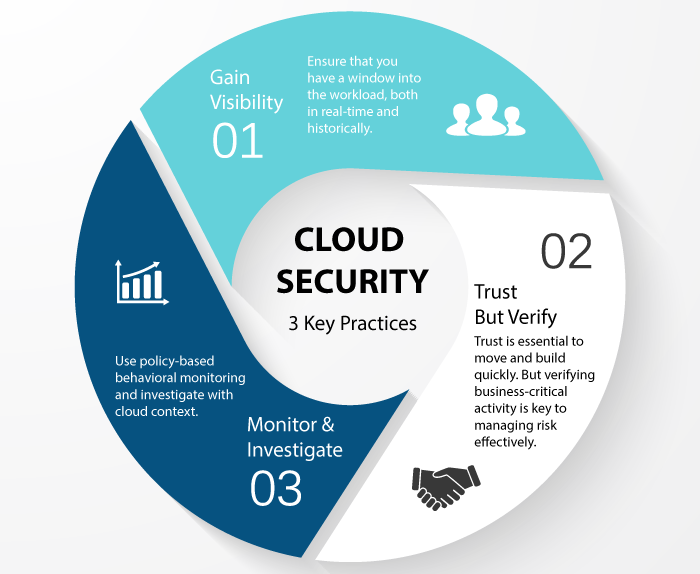
Existing security tools
SecuredCloud offers built in monitoring tools and integrates with existing MDM, DLP, event logging and backup tools, enabling existing tool chains to be used to monitor, back up and restore systems
Current security policies and processes
Thanks to the on-premise nature of Securedcloud and its ability to leverage existing data storage and database technologies, current security policies and governance processes can continue to be used to manage, control and secure operations with SecuredCloud.
Under Secured control
Control is key to security. With SecuredCloud, your IT department takes back control over its data, managed under its policies and procedures. SecuredCloud integrates in the tooling you use in your data center like logging and intrusion detection and works with existing authentication mechanisms like SAML, Kerberos and LDAP.
SecuredCloud features:
- Logging and monitoring
SecuredCloud has built in monitoring and logging tools, compatible with industry standard tools like Splunk, Nagios and OpenNMS. It also offers a full, compliance-ready activity log for reporting and auditing purposes. - Permission and File Access Control
Administrators can set permissions on sharing and access to files using groups. The powerful workflow tools in SecuredCloud enable administrators to limit access to files following strict rules and perform automatic actions like file conversion. - Encryption
SecuredCloud uses industry-standard SSL/TLS encryption for data in transfer. Additionally, data at rest in storage can be encrypted using a default military grade AES-256 encryption. Keys can be handled with the build in key management or you can opt for a custom key management for integration in existing infrastructure. As keys never leave the SecuredCloud server, external storage systems never have access to unencrypted data. - Virus scanning
SecuredCloud supports integration with ClamAV for automated scanning of all uploaded files.

Brute Force Protection
Brute Force Protection logs invalid login attempts and slows down multiple attempts from a single IP address (or IPv6 range). This feature is enabled by default and protects against an attacker who tries to guess a password from one or more users.
You can find more information on hardening your SecuredCloud installation in our extensive hardening guide
Password handling
Administrators can set password quality policies enforced by SecuredCloud.
Password reset tokens are invalidated when critical information like user email has been changed to protect against phishing attacks.
SecuredCloud will ask system administrators for password confirmation on security critical actions.
Security hardening
SecuredCloud employs a wide variety of extra security hardening capabilities, including:
- Content Security Policy 3.0CSP is a HTTP feature that allows the server to set specific restrictions on a resource when opened in a browser. Such as only allowing to load images or JavaScript from specific targets.CSP 3.0 is the latest, most strict version of the standard, increasing the barrier for attackers to exploit a Cross-Site Scripting vulnerability.
- Same-Site CookiesSame-Site cookies are a security measure supported by modern browsers that prevent CSRF vulnerabilities and protect your privacy further. SecuredCloud enforces the same-site cookies to be present on every request by enforcing this within the request middle ware.We include the __Host prefix to the cookie (if supported by browser and server). This mitigates cookie injection vulnerabilities within potential third-party software sharing the same second level domain.
Learn more about these hardening features in our blog.

Authentication capabilities
Authentication capabilities